The cybersecurity buzz from past weeks focused mostly on ransomware as far as cryptospace is concerned. Ransomware or repurposed ransomware that mines Monero are still the bulk of threats that are going around - but they also get most voice because it is the companies and servers that are concerned with this type of threat, not individuals.
However, the industry develops and just as couple years ago the darknet markets made it easy and affordable to purchase trojans, spyware and DDOS services from groups with customer support better than most legit software vendors, information stealers are now also becoming widely accessible.
Nocturnal stealer is a product sold via an online forum for 25 USD. If you thought nobody would bother with small fish like you hence you don’t need to bother with security, think again.
Democratizing Malware
This particular product comes with a user backend on a server owned by the authors of Nocturnal. If you pay for access you will get a user account and a package with the stealer to distribute but the package is already configured so that to get your stolen data you do not need to know how to code or how to admin a server.
The authors claim the server is unlikely to get seized and if it does, it does not collect user IP addresses so it should not be dangerous to use this, if you want to take their word for it. It is most likely though they archive the data they get through their customers and will probably first use it and then resell it. Proofpoint reports Nocturnal uses some quite high profile detection avoidance techniques which is uncommon in cheap products, the fact the Nocturnal people are the owners of their customers’ data could explain that.
They also offer customer support, minimum duration one month. I have to admin it looks pretty good, actually.
What Nocturnal Stealer Targets
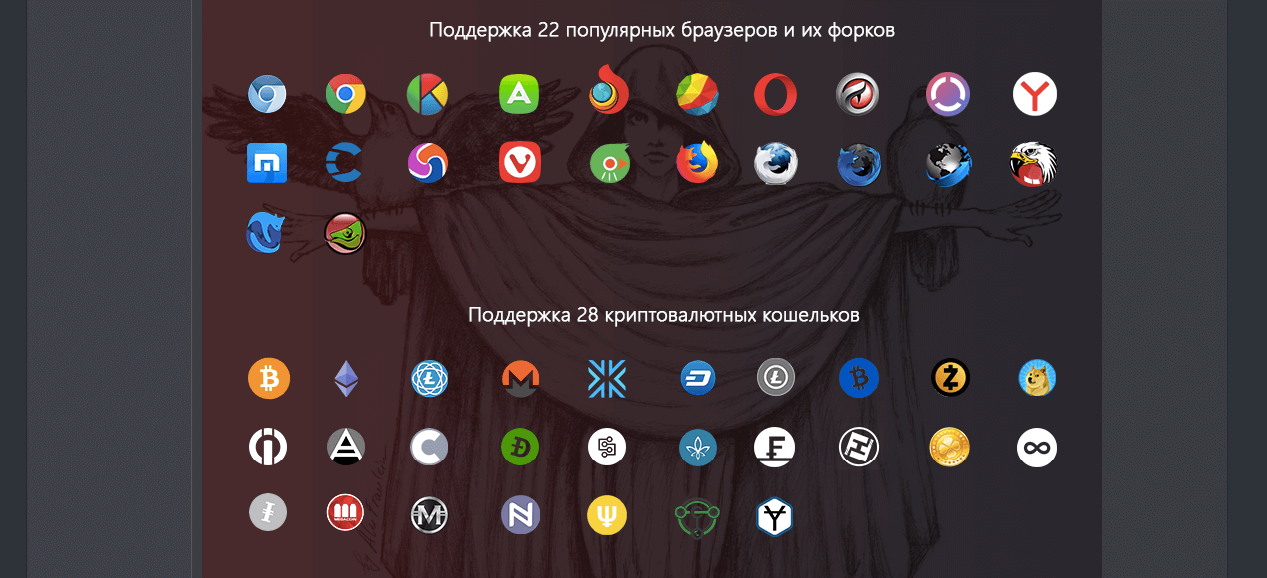
The stealer will first save your external IP, country code and similar information that can identify you in web traffic. Then it will scan your browsers for stored data, cookies, credit card information and autofills. It also collects FTP credentials form Filezilla and last but not least, wallet files and access data identified as related to mainstream cryptocurrencies:
Bitcoin Core, Ethereum, ElectrumLTC, Monero, Electrum, Exodus, Dash, Litecoin, ElectronCash, ZCash, MultiDoge, AnonCoin, BBQCoin, DevCoin, DigitalCoin, FlorinCoin, Franko, FreiCoin, GoldCoin, InfiniteCoin, IOCoin, IxCoin, MegaCoin, MinCoin, NameCoin, PrimeCoin, TerraCoin, and YACoin.
The disadvantage of this software is there is no operator with admin access to the victim, it is just a script so it won’t be able to find information that is well obfuscated on your hard drive. However, we all know most people don’t bother.
What you can do
As always, the best thing you can do is to make your crypto transactions from a computer you never use otherwise - thanks to the recent Drupal and other vulnerabilities malware is now spreading a lot through legitimate business websites where the company is cutting costs by not having fulltime webadmin staff and nobody knows it was necessary to apply a patch.
In 2018, you will not notice anything dodgy anymore.
Another part of the danger is the rising popularity of social engineering - you will not notice anything dodgy anymore in 2018.
There might be a normally looking software update prompt, you might also get an email with a PDF invoice. The idea is it will download the legitimate update or file or whatever it is and a trojan with it. The virus will collect some data, send it to a server and then delete itself to leave no trace. This type of attack solution makes 95% of all web attacks currently so it must be working quite well.
If you want to trust hardware wallets that’s a relatively reasonable way too, especially if you are transacting actively on the daily. Just remember they are a black-box, you don’t know what vulnerabilities they have.
Related post, as ever: Tiered Device Management for Crypto Holders